We Had This Argument in 1995: Restricting Cybersecurity AI Is a Losing Game
Gated cyber models may buy defenders time, but history suggests the advantage will not last.
Gated cyber models may buy defenders time, but history suggests the advantage will not last.
AI coding tools and autonomous agents are shipping faster than the guardrails meant to govern them. Here is where the risks are and what thoughtful adoption looks like.
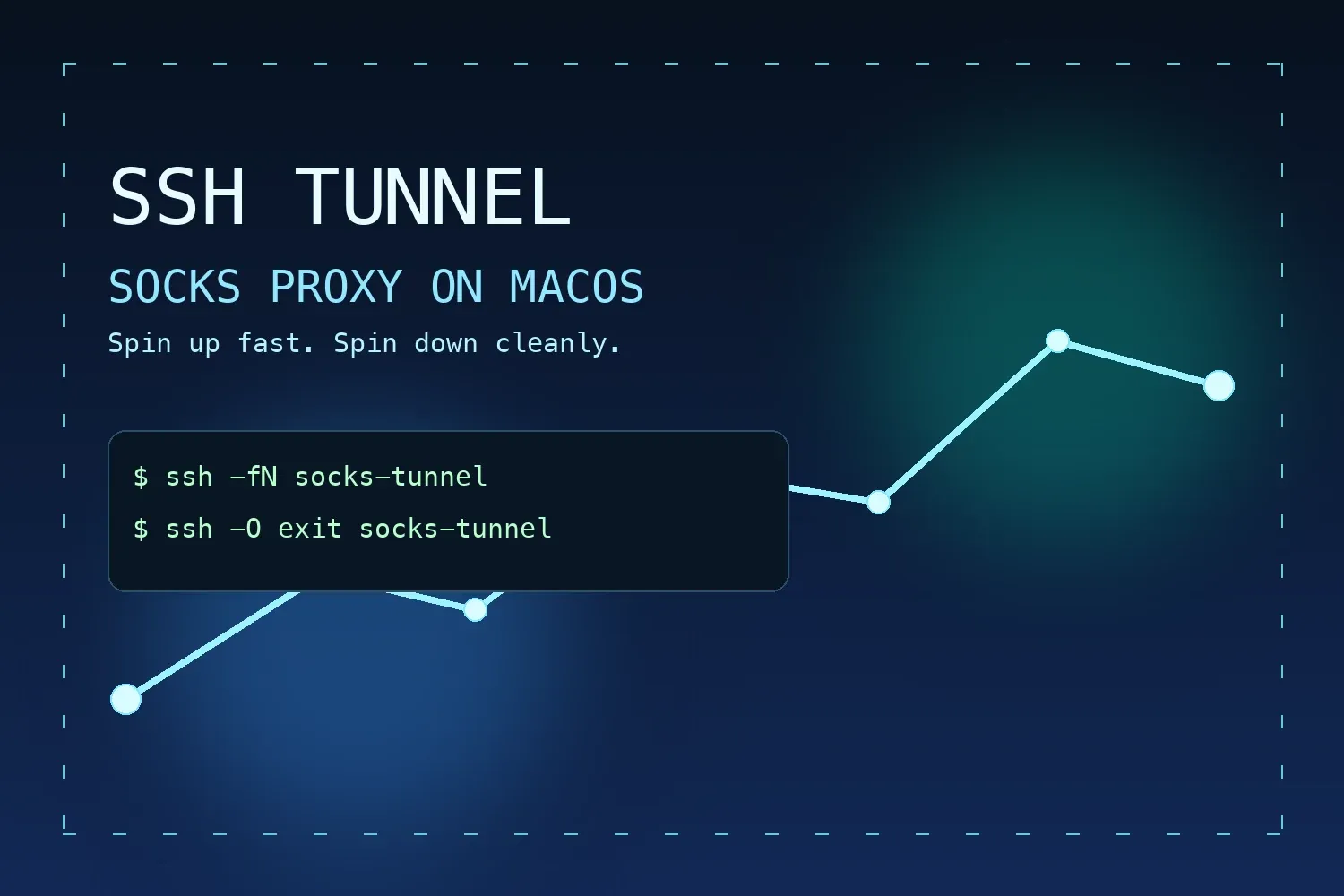
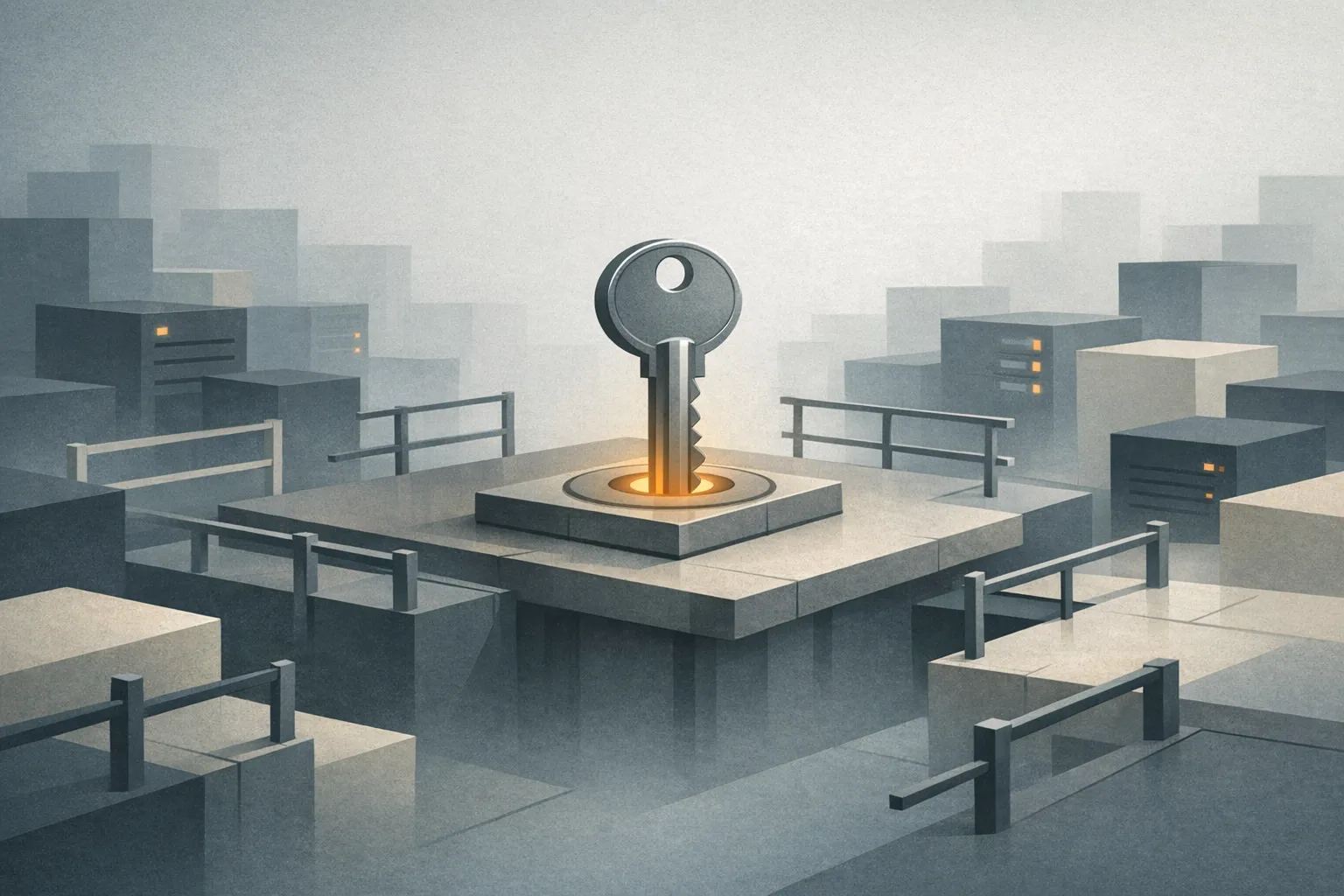
Create a secure, temporary SOCKS proxy from your Mac with SSH dynamic port forwarding and simple start/stop commands.

The repeat mistakes that still leak API keys, tokens, and credentials into Git and logs, plus practical fixes.

Use a simple .git/hooks/pre-commit script to block secrets before they land in history.
Exploring the dual nature of AI code assistants, their benefits, risks, and how to use them responsibly.

Configuration guide for Nginx to achieve an A+ SSL rating, including cipher suites and Diffie-Hellman parameters.

A guide to generating SSH keys and configuring passwordless authentication between servers.